Secure Document Sharing Built for Law Firms
SpaceNexus provides secure document sharing purpose-built for law firms and legal teams. Protect attorney-client privilege, manage structured due diligence Q&A workflows, and maintain tamper-evident audit logs — all within a SOC 2 Type II certified Virtual Data Room platform that courts and regulators accept.
Whether your firm handles M&A transactions, litigation discovery, corporate restructuring, or IPO preparation, SpaceNexus delivers the security infrastructure and compliance certifications that legal oversight committees demand.
Trusted by law firms worldwide — certified and compliant
Why law firms need a dedicated Virtual Data Room
Law firms operate under unique regulatory and ethical obligations that generic file-sharing platforms were never designed to address. When attorneys share documents through consumer-grade tools like Dropbox, Google Drive, or email attachments, they risk inadvertent waiver of attorney-client privilege, loss of work-product protections, and regulatory violations that can result in sanctions, malpractice claims, or disqualification from proceedings.
A dedicated legal Virtual Data Room like SpaceNexus solves these problems by providing the infrastructure that legal workflows demand: separate privilege and non-privilege folder hierarchies, tamper-evident audit trails that courts accept as evidence, dynamic watermarking that deters and traces leaks, NDA click-through gates that enforce confidentiality before any materials are viewed, and granular access controls that let administrators restrict access down to the individual document level.
For firms managing M&A due diligence, litigation discovery, or multi-party corporate transactions, the difference between a general-purpose cloud storage platform and a purpose-built legal VDR is the difference between compliance and exposure. SpaceNexus was designed from the ground up for the security standards, audit requirements, and privilege protections that law firms and their oversight committees require.
Security features built for the standards law firms require
Every feature in SpaceNexus was designed with legal privilege, regulatory compliance, and courtroom admissibility in mind. Here is how we protect your firm and your clients.
Attorney-Client Privilege Protection
Separate privilege and non-privilege document sets with granular folder-level permissions. Dedicated privilege log management ensures only authorized attorneys access protected materials, preventing inadvertent waiver during due diligence proceedings.
Tamper-Evident Audit Logs
Every document access, download, print, and permission change is logged with cryptographic certainty. Audit logs are immutable, timestamped to the millisecond, and generate court-admissible reports that regulators and judges accept as evidence of compliance.
Dynamic Watermarking
Every downloaded or printed document is automatically watermarked with the recipient's name, email, IP address, and timestamp — deterring unauthorized sharing and enabling immediate leak source identification if confidential materials surface externally.
Granular Access Control
Role-based permissions at the document, folder, and individual user level. Set automatic access expiry dates, restrict downloads per party, limit printing, enforce view-only modes for sensitive materials, and revoke access instantly when engagement terms change.
NDA Click-Through Gate
Require every external party to sign an NDA or confidentiality agreement before accessing any data room materials. Signed agreements are automatically stored with timestamps, IP addresses, and digital signatures in the deal record for future reference.
SOC 2 Type II Certification
SpaceNexus is independently audited and SOC 2 Type II certified, with ISO 27001 alignment and GDPR readiness. Client data is protected by AES-256 encryption at rest, TLS 1.3 in transit, and infrastructure hosted in SOC 2 certified data centers with 99.9% uptime SLA.
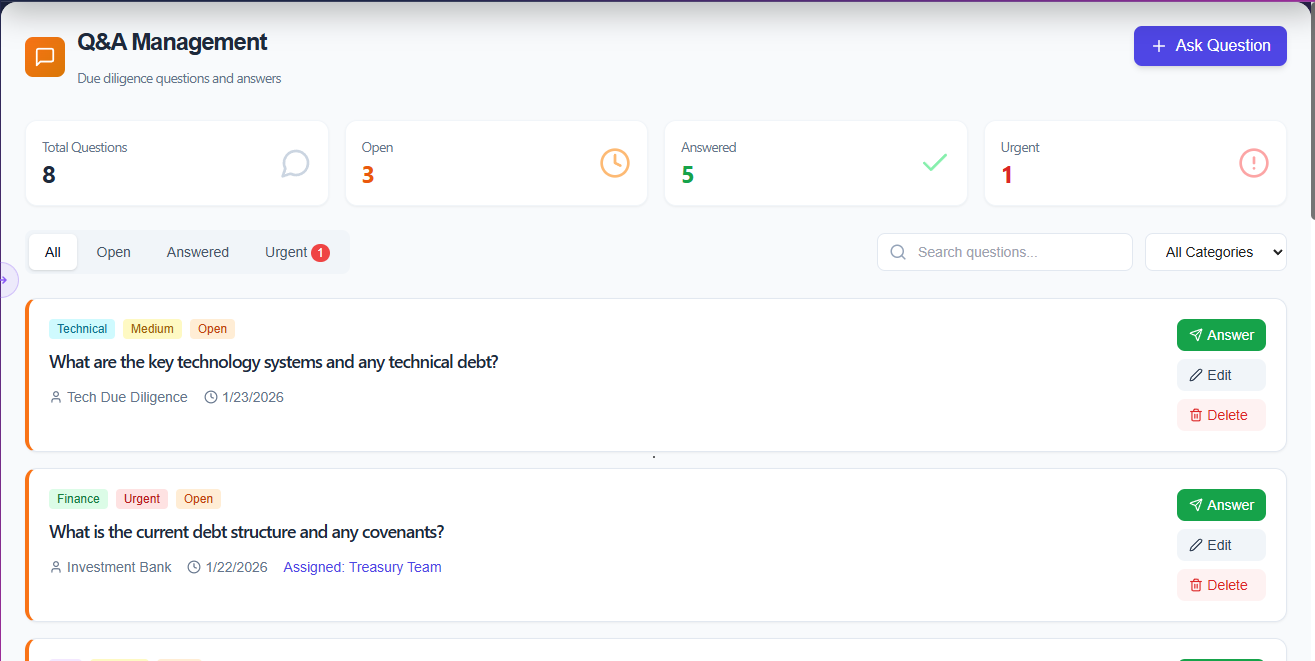
Structured Q&A — engineered for legal due diligence
The SpaceNexus Q&A module transforms how law firms handle due diligence communication. Instead of scattered email threads where privilege risks multiply, every question and response lives in a centralized, auditable workspace.
Questions are categorized by department (Finance, Legal, Technical, Commercial), flagged by urgency, and assigned to the right subject matter expert. Every response is version-controlled with a full audit trail. No more hunting through email chains — and no risk of inadvertent waiver of privilege through misdirected responses.
- Privilege log visible only to authorized attorneys
- Finance / Legal / Technical / Commercial category tags
- Urgency flags with visual status indicators
- Full Q&A audit trail for regulator review
- Version-controlled responses with edit history
- Bulk export of Q&A logs for closing binders
SpaceNexus vs. generic cloud storage vs. legacy data rooms
See how SpaceNexus compares to consumer file-sharing tools and traditional data room providers on the features that matter most to law firms.
| Feature | SpaceNexus | Generic Cloud Storage | Legacy Data Rooms |
|---|---|---|---|
| Attorney-Client Privilege Folders | |||
| Tamper-Evident Audit Logs | |||
| Dynamic Watermarking | |||
| NDA Click-Through Gate | |||
| Granular Folder-Level Permissions | |||
| Structured Q&A with Audit Trail | |||
| SOC 2 Type II Certified | |||
| ISO 27001 Aligned | |||
| AI-Powered Document Processing | |||
| Real-Time Activity Analytics | |||
| Unlimited Users & Storage | |||
| 24-Hour Data Room Setup |
How to set up a secure legal data room in four steps
Most law firms have their SpaceNexus data room operational within 24 hours. Here is the typical setup workflow for legal teams.
Set Up Your Secure Legal Data Room
Create a new data room in minutes. Define your folder structure with separate privilege and non-privilege hierarchies, upload documents in bulk with drag-and-drop, and let AI auto-index your files by category.
Configure Access & NDA Requirements
Invite deal parties, opposing counsel, or client teams. Set granular permissions at the folder and document level, enable NDA click-through gates, and configure access expiry dates for each party.
Manage Due Diligence Q&A
Buyers or opposing counsel submit questions directly in the data room. Questions are routed by department (Finance, Legal, Technical), assigned to subject-matter experts, and tracked from Open through to Answered with full version control.
Monitor Activity & Generate Reports
Track every document view, download, and print in real-time. Generate court-admissible audit reports, identify which parties have reviewed which materials, and export compliance-ready logs for regulators or oversight committees.
Legal use cases for secure document sharing
From billion-dollar M&A transactions to routine corporate filings, law firms use SpaceNexus across every practice area that involves confidential document exchange.
M&A Transaction Counsel
Manage buyer and seller document flows across multiple deal parties — with separate privilege sets, controlled Q&A, complete closing binder archiving, and real-time visibility into buyer engagement with key transaction documents.
Learn moreLitigation & E-Discovery
Share discovery documents with opposing counsel under court-mandated protective orders. Tamper-evident audit logs demonstrate compliance with production requirements, and dynamic watermarking deters unauthorized distribution of sensitive materials.
Learn moreCorporate Transactions
Real estate closings, joint ventures, licensing agreements, and corporate restructuring — all require controlled document sharing where privileged materials are protected throughout the transaction lifecycle with full regulatory audit trails.
Learn moreIPO & Capital Markets
Prepare and share prospectus drafts, financial statements, and regulatory filings with underwriters, auditors, and legal advisors in a secure environment that meets SEC and financial regulatory requirements.
Learn moreFrequently asked questions about secure legal document sharing
What is secure document sharing for law firms?
Secure document sharing for law firms is a specialized Virtual Data Room (VDR) platform that allows attorneys to share confidential documents with clients, opposing counsel, and deal parties while maintaining attorney-client privilege. Unlike generic file-sharing tools, a legal VDR provides granular access controls, tamper-evident audit trails, dynamic watermarking, and NDA gates — all features required for regulatory compliance and courtroom admissibility.
How does SpaceNexus protect attorney-client privilege?
SpaceNexus protects attorney-client privilege through dedicated privilege and non-privilege folder hierarchies with separate permission sets, ensuring only authorized attorneys can view protected materials. Privilege logs are maintained automatically, access is restricted at the document, folder, and user level, and every interaction is recorded in an immutable audit trail — preventing inadvertent waiver of privilege during due diligence.
Is SpaceNexus compliant with SOC 2, ISO 27001, and GDPR?
Yes. SpaceNexus is independently audited and SOC 2 Type II certified. The platform aligns with ISO 27001 information security standards and is GDPR-ready for firms operating in or with European clients. All data is encrypted with AES-256 at rest and TLS 1.3 in transit, with data residency options available to meet jurisdictional requirements.
How is a legal VDR different from Dropbox or Google Drive?
Generic cloud storage like Dropbox or Google Drive lacks the security controls law firms require: there are no granular permission hierarchies, no tamper-evident audit logs accepted by courts, no dynamic watermarking, no NDA click-through gates, and no privilege log management. A legal VDR like SpaceNexus is purpose-built for regulated industries where document security, access control, and compliance are non-negotiable.
What types of legal transactions use SpaceNexus?
SpaceNexus is used for M&A due diligence, litigation and e-discovery document production, corporate restructuring, IPO preparation, real estate closings, joint ventures, and licensing agreements. Any legal workflow that involves sharing confidential or privileged documents with external parties benefits from a secure, audit-ready data room.
Set up a secure legal data room today
SOC 2 Type II certified. ISO 27001 aligned. AES-256 encryption. Tamper-evident audit logs. Dynamic watermarking. NDA gates. Everything your firm's oversight committee requires — operational within 24 hours.
SOC 2 Type II · ISO 27001 · GDPR · AES-256 · TLS 1.3 · Dynamic watermarking · NDA gate